how to tell the difference
Extra visitors ought to imply extra success, however in apply, it usually doesn’t. Many web sites see rising go to counts whereas conversions, engagement, and income stay flat, leaving groups questioning why “progress” doesn’t really feel like progress in any respect.
One motive is that not all visitors represents actual individuals. Automated exercise now makes up a big share of the trendy net. The truth is, the 2025 Imperva Bad Bot Report discovered that automated methods accounted for 51% of all net visitors in 2024, that means bots collectively generated extra requests than human guests for the primary time in a decade.
When automated visitors mixes into analytics reviews, uncooked go to counts alone grow to be an unreliable measure of actual viewers curiosity or demand.
This text explains the right way to distinguish between real web site guests, useful automation, and dangerous bot exercise.
What bot visitors really is
Bot visitors refers to requests made by automated software program slightly than by a human utilizing a browser. These packages ship requests to net pages, pictures, scripts, or APIs in the identical means a customer’s browser would, however the exercise occurs with out direct human interplay.
From a technical standpoint, the server usually sees the identical sort of request. The distinction lies in how the request is generated and the way it behaves over time.
Automation just isn’t uncommon or inherently dangerous. A lot of the web is dependent upon automated methods that constantly crawl web sites, test uptime, validate efficiency, or retrieve knowledge for reliable providers. Engines like google depend on bots to find and index new content material, monitoring instruments often check availability, and varied integrations question APIs to maintain functions synchronized.
Importantly, the phrase “bot” describes how the visitors is generated, not why it exists. Some automated methods assist visibility and safety, whereas others try to use vulnerabilities, scrape content material, or overwhelm infrastructure. As a result of intent varies broadly, figuring out and classifying bot conduct is much extra helpful than treating all automated visitors as a single class.
The three forms of visitors hitting your web site
Web site visitors is commonly mentioned as a easy break up between “human” and “bot,” however in actuality, most requests fall into three sensible classes: actual guests, useful bots, and dangerous bots. Understanding this distinction makes it simpler to interpret analytics, handle assets, and apply the proper safety controls with out disrupting reliable exercise.
As we talked about earlier, the Imperva Dangerous Bot Report famous that automated visitors accounted for greater than half of all net requests globally, with a considerable portion categorized as both helpful automation or malicious bot exercise. When these completely different sources are mixed, visitors quantity alone offers little perception into actual consumer demand or engagement.
The purpose is to not block something that seems automated, however to determine which requests are from actual individuals, which assist web site performance and visibility, and which create danger or pointless load.
Analyzing conduct patterns, request traits, and visitors sources can provide the readability wanted to permit helpful automation, shield in opposition to dangerous exercise, and consider efficiency utilizing knowledge that displays real user behavior.
Actual guests: What human visitors appears like
Human visitors tends to comply with irregular, unpredictable patterns. Actual guests transfer by websites in various methods. They click on completely different navigation paths, pause on sure pages, scroll at completely different depths, and spend inconsistent quantities of time earlier than taking the subsequent motion. Even when a number of guests arrive from the identical marketing campaign or area, their conduct not often follows an identical sequences.
Genuine consumer classes additionally embody lifelike interplay patterns. Actions like on-site searches, form submissions, media playback, account logins, or e-commerce exercise sometimes happen in logical progressions slightly than in completely timed or repeated intervals. The timing between requests varies naturally, reflecting how individuals learn, assume, and resolve what to do subsequent.
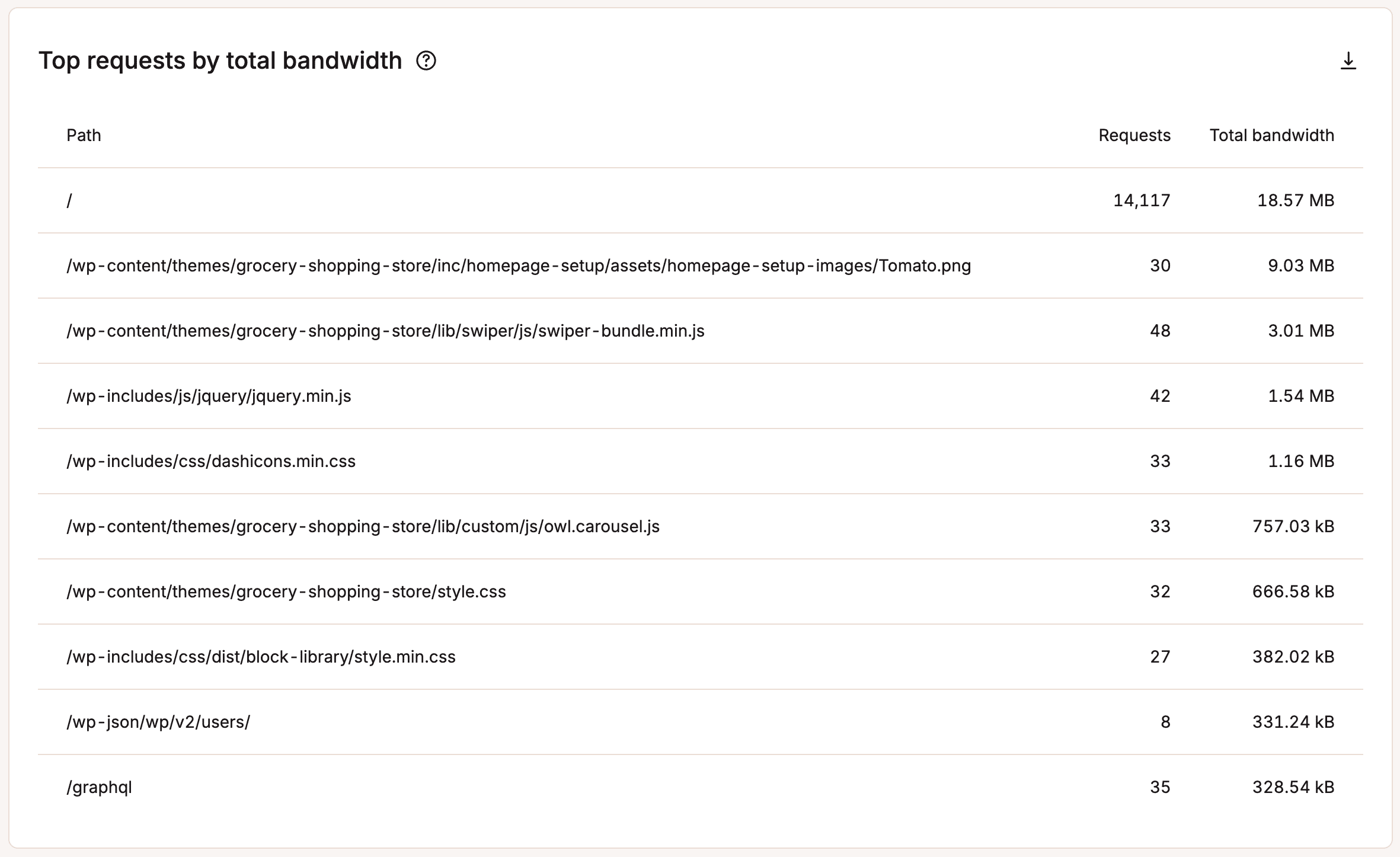
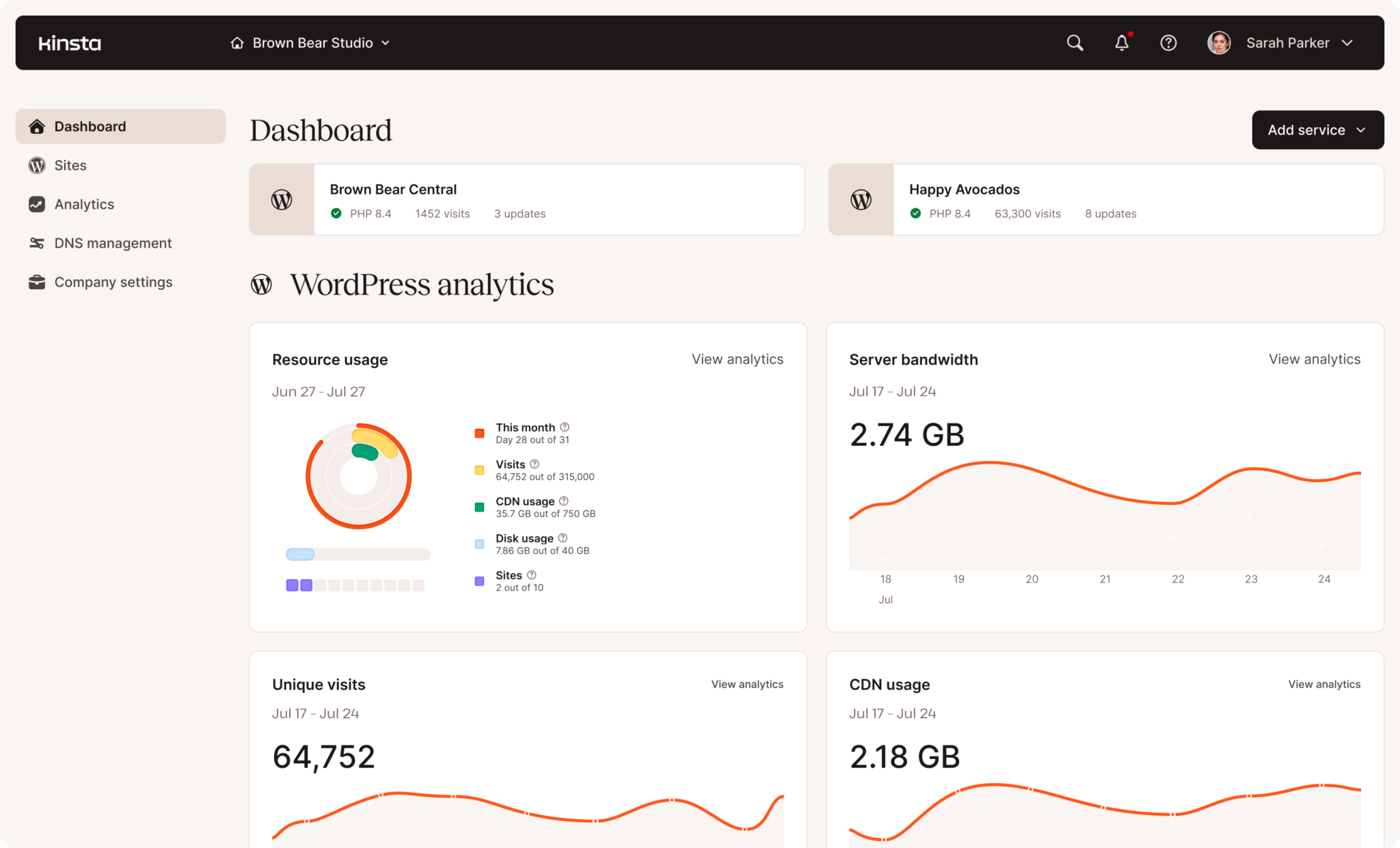
With MyKinsta, you possibly can rapidly see which pages are getting probably the most visitors, at a look:
Machine variety is one other robust indicator of human visitors. Actual guests arrive utilizing a large mixture of browsers, working methods, connection speeds, and display screen sizes. Even concentrated geographic visitors exhibits variation throughout units and configurations, making a distribution that not often seems uniform.
MyKinsta offers data on system use as properly:
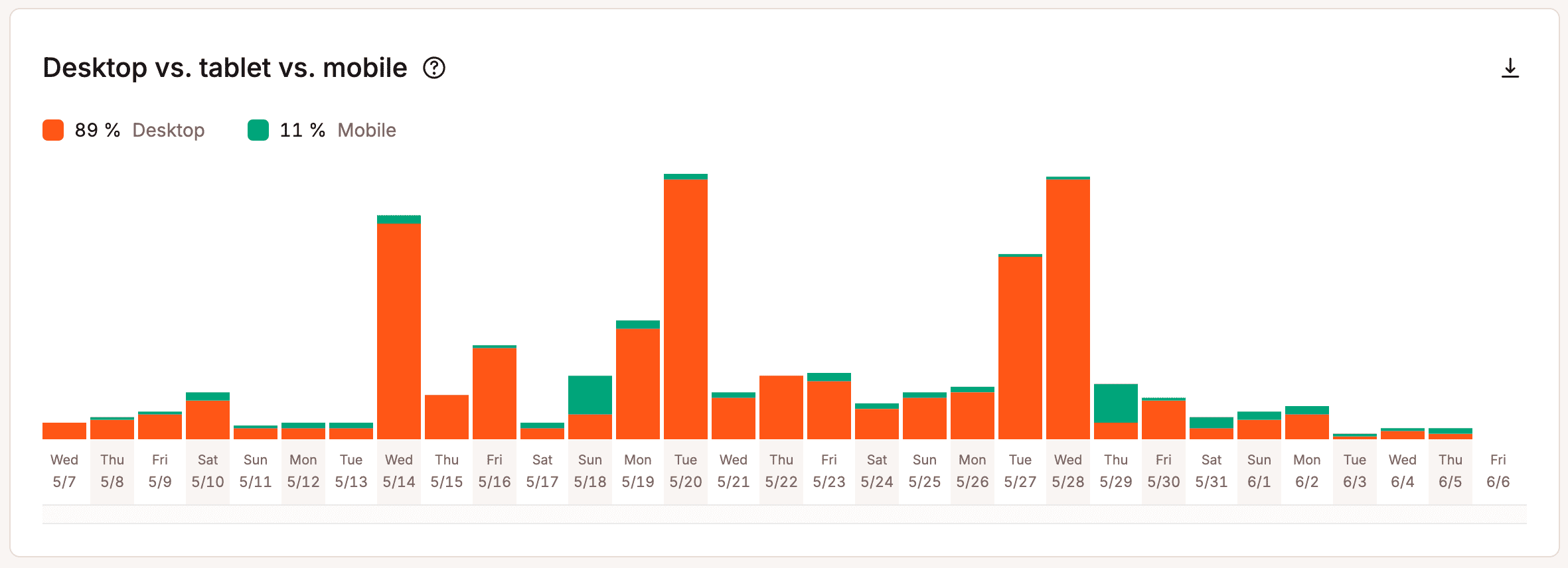
On the similar time, figuring out human visitors just isn’t all the time simple. Privacy protections, advert blockers, caching layers, and shared community environments can obscure sure alerts or make completely different customers seem comparable on the infrastructure stage.
For that reason, visitors classification works greatest when a number of indicators, together with these conduct patterns, session traits, system variety, and interplay alerts we talked about are evaluated collectively slightly than counting on any single metric alone.
Useful bots: Automation that helps your web site
Not all automated visitors is one thing you wish to cease. Many bots play a necessary position in retaining your web site seen, monitored, and functioning appropriately.
Search engine crawlers
This is without doubt one of the most vital examples. These bots systematically request pages to find new content material, consider adjustments, and replace search indexes.
Their conduct is usually structured and predictable, following hyperlinks methodically and respecting crawl directives outlined in robots.txt. Stopping these crawlers from accessing your web site can cut back search visibility and delay how rapidly new pages seem in outcomes.
Uptime screens and testing providers
Different reliable automation focuses on monitoring and operational well being. Uptime monitoring instruments, efficiency checkers, and artificial testing providers ship requests at common intervals to substantiate availability, measure load occasions, and detect failures early.
web optimization and validation instruments
Equally, web optimization, accessibility, and validation instruments scan pages to determine technical points, broken links, or compliance issues that would in any other case go unnoticed.
Useful bots usually make their presence clear. They usually determine themselves by constant consumer agent strings, function inside outlined request limits, and comply with revealed crawl insurance policies.
As a result of these methods assist indexing, observability, and integrations, blocking them with out overview can interrupt monitoring workflows, cut back discoverability, or break providers that rely upon scheduled automated requests.
Dangerous bots: Site visitors that creates danger or waste
Dangerous bots are automated methods designed to use web sites, extract knowledge at scale, or devour infrastructure assets with out offering any reliable worth. In contrast to useful automation, these bots sometimes try to disguise their id, ignore crawl guidelines, and generate request patterns meant to bypass primary protections.
Credential-stuffing and brute-force bots
These are among the many commonest threats. These methods repeatedly goal login endpoints, testing massive lists of stolen usernames and passwords in fast succession in an try to achieve unauthorized entry. Even when unsuccessful, the amount of requests can enhance server load and sluggish response occasions for reliable customers.
Vulnerability scanners and scrapers
Different malicious automation focuses on discovery and exploitation. Vulnerability scanners probe identified directories, configuration information, and software program endpoints to seek for outdated elements or misconfigurations that might be exploited. Aggressive scraping bots might also request massive volumes of pages or media information to repeat content material for republishing elsewhere, consuming bandwidth and infrastructure capability within the course of.
DDoS assaults
Some assaults goal purely at disruption slightly than entry. Site visitors-flooding and denial-of-service campaigns try to overwhelm servers or software layers with sustained request spikes, degrading efficiency or making providers briefly unavailable.
Past its speedy efficiency impression, dangerous bot visitors can distort analytics and degrade the expertise for actual guests if left unmanaged.
Tips on how to inform people, useful bots, and dangerous bots aside
Distinguishing between actual guests, useful automation, and dangerous bots relies upon much less on any single identifier and extra on recognizing constant conduct patterns throughout a number of alerts.
When evaluated collectively, these indicators make it simpler to find out whether or not visitors displays human exercise, reliable automation, or doubtlessly abusive requests.
Request frequency and timing
Human guests generate requests at irregular intervals as they learn, scroll, and navigate, whereas automated methods are inclined to request pages at extremely constant speeds or in fast bursts that will be tough for an individual to duplicate. Extraordinarily excessive request charges from a single supply or completely timed intervals normally point out scripted exercise.
Consumer agent strings
Legit bots sometimes determine themselves clearly and persistently, whereas dangerous bots ceaselessly rotate or spoof consumer brokers in an try to seem human. Evaluating consumer agent declarations with noticed conduct helps reveal inconsistencies that point out there’s automation.
IP popularity and community possession
Site visitors originating from identified cloud internet hosting networks, proxy providers, or beforehand flagged addresses might point out automated methods slightly than from actual individuals. Popularity databases and safety instruments classify these networks primarily based on previous exercise and assist to determine suspicious sources extra rapidly.
Geographic distribution patterns
Sudden will increase in visitors from sudden areas, particularly when mixed with an identical request conduct, might recommend coordinated bot exercise slightly than real viewers progress.
Respect for robots.txt and crawl limits
If you happen to discover this, it’s a robust indicator of reliable automation. Useful bots usually comply with revealed crawl insurance policies and function inside affordable request limits, whereas dangerous bots sometimes ignore these directives and proceed to request restricted paths or information.
As a result of none of those alerts alone offers a whole reply, efficient classification comes from analyzing a number of indicators collectively. Over time, these mixed patterns create a dependable image of whether or not incoming visitors represents actual customers, helpful automation, or exercise that requires filtering or mitigation.
The place to research bot visitors
Understanding bot exercise requires visibility throughout a number of layers of your internet hosting and supply stack. No single instrument exhibits the entire image, which is why combining analytics, logs, and safety dashboards produces much more dependable insights. Let’s check out every:
Analytics platforms present a high-level place to begin
Site visitors spikes with out matching engagement, sudden geographic anomalies, or uncommon system distributions usually sign automated exercise. Whereas analytics instruments don’t all the time classify bots exactly, they assist illustrate patterns that sign a necessity for deeper investigation. Even easy plugins like Jetpack can help with this.
Server and entry logs provide probably the most detailed view of request conduct
Logs reveal request frequency, response codes, consumer agent strings, IP addresses, and accessed paths, which allow you to to determine repeated scanning patterns, login assault makes an attempt, or scraping conduct that will in any other case stay hidden in analytics knowledge that’s all aggregated collectively.
CDN dashboards add one other layer of visibility
CDN dashboards present visitors patterns on the community edge earlier than requests attain your origin server. These dashboards usually spotlight traffic surges, regional anomalies, or repeated automated requests which might be filtered or rate-limited upstream. This helps you detect assaults a lot sooner than you’ll in any other case.
Firewalls and WAF instruments present real-time perception
Firewalls allow you to study blocked, challenged, or suspicious requests in real-time. Reviewing firewall logs can reveal which visitors sources are triggering safety guidelines and whether or not changes are wanted to cut back false positives or tighten protections.
Managed hosting platforms simplify the method by consolidating a number of of those knowledge sources. For instance, environments that combine CDN-level analytics, firewall monitoring, and entry logs right into a single dashboard make it simpler to correlate suspicious conduct throughout layers.
Internet hosting suppliers like Kinsta additionally spotlight visitors analytics, efficiency monitoring, and safety occasion knowledge instantly inside their dashboard, MyKinsta. This implies you and your workforce can analyze bot behavior with out having to depend on a number of exterior instruments.
How bot visitors distorts analytics and decision-making
When automated requests combine with reliable visits, analytics knowledge begins to replicate exercise that doesn’t characterize actual viewers curiosity. Pageviews and session counts might seem to rise steadily regardless that precise engagement, conversions, or income stay unchanged. With out separating automated visitors from human classes, you could interpret inflated visitors numbers as progress and make strategic selections primarily based on deceptive alerts.
Engagement metrics grow to be particularly unreliable. Bots usually generate classes with extraordinarily brief durations, speedy exits, or repeated web page requests, which might artificially enhance or lower bounce rate and time-on-page measurements. In some circumstances, scraping bots repeatedly request particular pages, creating the looks that sure content material performs much better than it really does amongst actual customers.
Geographic, system, and referral knowledge might also grow to be distorted. Automated visitors ceaselessly originates from knowledge facilities, proxy networks, or concentrated areas that don’t match the positioning’s precise buyer base. When these classes are included in reviews, advertising and marketing groups might put money into the incorrect areas, optimize for incorrect system tendencies, or misread campaign performance.
Over time, these inaccuracies have an effect on reporting, efficiency planning, infrastructure scaling selections, and advertising and marketing investments. All of those attributes depend on traffic analytics to foretell demand. If a good portion of that visitors consists of automated requests, companies danger overestimating progress, allocating assets inefficiently, or overlooking actual user behavior that requires consideration.
Finest practices for managing various kinds of visitors
Managing fashionable net visitors requires a balanced method that protects web site efficiency with out interfering with reliable automation or actual customers. Slightly than trying to dam something that seems automated, the purpose is to use insurance policies that match the conduct and intent of every visitors sort.
Prioritize actual consumer expertise
Optimize efficiency, availability, and accessibility so reliable guests can entry content material rapidly and reliably, even throughout visitors spikes. Quick load occasions, secure infrastructure, and resilient caching assist make sure that reliable customers should not affected when automated visitors will increase. You possibly can optimize for efficiency instantly inside Kinsta through the use of Kinsta API with Google PageSpeed Insights.
Enable and monitor useful automation
Search engine crawlers, uptime monitors, and validation instruments ought to be explicitly allowed the place acceptable so indexing, monitoring, and integrations proceed to perform appropriately. Reviewing crawl conduct periodically helps verify that reliable bots function inside affordable limits.
Apply behavior-based protections to dangerous visitors
Rate limits, safety challenges, and focused blocking guidelines work greatest when triggered by suspicious request patterns slightly than static assumptions about IP ranges or consumer brokers. Behavioral controls cut back the probability of blocking reliable providers whereas nonetheless mitigating abusive exercise.
Assessment and alter insurance policies often
Site visitors patterns change as websites develop, campaigns launch, and new automated methods work together with content material. Periodic critiques of firewall guidelines, charge limits, and monitoring alerts assist make sure that protections match your present visitors conduct as a substitute of counting on outdated assumptions.
Use visitors supply info to make higher selections
Site visitors quantity alone not often tells the total story of how a web site performs. When human visits, useful automation, and dangerous bot exercise are separated, analytics knowledge turns into much more significant and actionable.
Clear visitors segmentation permits groups to measure real viewers progress, perceive actual engagement patterns, and consider advertising and marketing efficiency with out automated noise distorting the outcomes.
Extra correct visitors classification additionally improves operational selections. Efficiency planning, infrastructure scaling, and safety methods grow to be simpler to align with actual demand when automated requests are measured and managed independently.
In case your present internet hosting atmosphere offers restricted visibility into visitors sources, it might be price evaluating platforms that provide deeper visitors intelligence and built-in bot administration instruments. Managed environments like Kinsta present built-in analytics, firewall protections, and edge-level visitors insights that assist distinguish actual customers from automated activity.
Kinsta’s newer bandwidth-based hosting plans additionally add flexibility by extra intently pairing internet hosting assets with precise visitors consumption. In case you have questions, you possibly can talk to our support team anytime.
Post Views: 41